Cyber threats are on the loose, with instances of data breaches and identity theft being common news nowadays. Although the proliferation of the internet has improved our means of communication, it has also brought alongside it a surge in cybercrime. Therefore, tapping into the right tools to protect our privacy and enhance our security while online is paramount.
In this article, we’ll take a look at one such tool — proxies, a robust protection mechanism designed to shield data and digital assets online. With 2024 seeing an alarming surge in cyber attacks, it stands to reason that businesses and individuals would want to seek ways to shield themselves. Worry not because in this write-up, we’ll elucidate everything you need to know.
Online Proxy Tools to Boost Your Defenses
![]()
Proxy servers are crucial for those endeavoring to escalate their online security measures. At their core, they are nothing more than an intermediary server that relays requests between your devices and the internet. Instead of connecting you directly to websites and services, what a proxy does is handle requests in your stead. This action effectively masks your IP address, a unique identifier over the internet, cloaking your online presence.
They are an indispensable tool for safeguarding one’s online activities. Considering how data-driven the world has become today, employing these proxies should be at the forefront of anyone looking to boost their defenses and privacy while surfing the web.
Advantages of Online Proxies

Tapping into these systems allows users to gain a wealth of benefits. Among those, the most important worth highlighting are:
- Geo-Block Circumvention: Proxies enable users to bypass geoblocking restrictions set forward by websites and services. For fighting against censorship or accessing content that might be unavailable in your region for one reason or another, these tools are the way to go.
- Content Filtering and Malware Protection: These systems also prove exceptional when enforcing content filtering policies within networks. They can intercept and inspect any web traffic to block access as needed if they detect anything unusual.
- Improved Remote Access: Ensuring access to remote workforces is vital in this day and age, and proxies ensure just do that. They can act as a protective gateway between remote users and internal networks, authenticating and encrypting data as needed.
- Service Optimization: Thanks to load balancing, proxies prevent server overload and boost website performance. They can also cache content, compress data, and prioritize traffic based on certain policies, all measures that reduce latency and bandwidth consumption.
Safeguarding Through Encryption
When it comes to heightening online security, encryption is a process that helps out a lot. What it does is encode information so that only authorized parties can access it. It can secure anything, from personal messages to financial transactions. In case a third party happened to steal the data, they would be unable to decipher the gibberish on their end due to the encryption. This process guarantees not only data transmission but also confidentiality and data integrity.
Some proxies can make use of encryption to add an extra layer of security to communications. What they do with this is encrypt the data as it passes through them. This multi-layered protection for the data in transit is a combo that makes it almost impossible for hackers to track and intercept, effectively shielding users online.
Best Practices to Follow
![]()
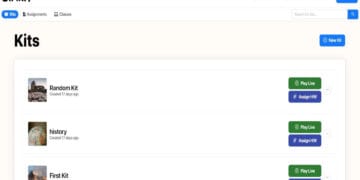
Knowing how fundamental online proxy tools are to protect privacy and enhance security, the next step would be ascertaining the one you need. Your selection should follow providers known for their strong reputations, solid track records, and clear privacy policies. You should look for services that employ state-of-the-art encryption protocols and keep no logs whatsoever. Moreover, the very best services often have security audits and transparency reports.
Making use of additional measures, such as secure browsers like Brave or Tor, or installing ad-blockers and script-blockers can also go a long way in keeping you safe online. Try to also adjust your actions depending on how sensitive they are. For example, simple precautions may work perfectly fine for daily surfing, but for accessing financial accounts, you may need to employ a higher level of security. Finally, don’t forget to periodically re-evaluate your privacy needs in response to changes.
Conclusion
Bolstering your online safety is what proxies excel at. For protecting privacy and enhancing security, these tools come second to none in their convenience and effectiveness. They not only help users to anonymize their online identities, but they can also prove crucial to circumvent geo-blockades, filter malicious content, and optimize network performance.
Whether you want to use them for personal privacy protection or business security, proxies are indispensable tools in safeguarding the integrity and confidentiality of online communications. Looking to find out which one is the best for you? Why not use this online proxy checker to discover more about these tools?